nobeastsofierce - Fotolia
What are 3 cloud backup security guidelines against cyberattacks?
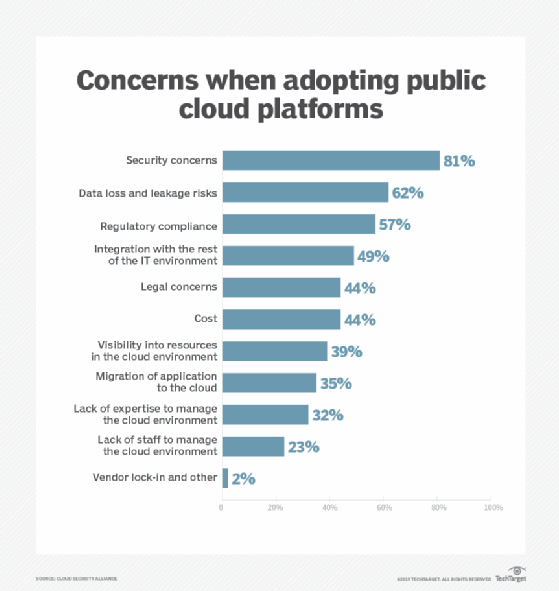
Cloud security is a top concern for IT. As a result, keeping cloud backups secure should be a priority. Here are three straightforward guidelines to help.
Cloud backup security best practices aren't too different from those of on-premises backups. Especially with cyberthreats a constant presence in IT, it is important to practice defense in depth, just as you would for backups residing on premises.
The first -- and, arguably, most important -- element of cloud backup security is encryption. Your data needs to be encrypted both at rest and in flight. Protecting data at rest refers to the use of storage-level encryption. Protecting data while it is in flight means using encryption to protect your data as it is being transmitted across the network and, ultimately, to the cloud-based backup target.
A second best practice for cloud backup security is isolating the data. At the very least, it is a good idea to store backup data in a separate storage bucket from the data that your backup is protecting. That way, if a bucket's contents become corrupted or are attacked by malware, the event won't immediately impact the backup target.
Keep in mind that simply backing up your data to a separate storage bucket offers minimal protection. Ideally, you should write backups to storage that is associated with a different account, preferably in a different cloud. This approach guards your backups against a situation in which either your primary account, or even the cloud itself, is compromised. The backups are securely stored within a different account.
Even if your cloud's root account is never compromised, storing data in a separate account improves cloud backup security because it prevents any of your users from accidentally being granted permission for the backup storage bucket.
Finally, keep your backup server and your protected applications up to date. Backup servers are a favorite target for hackers, because compromising a backup server can provide access to all of the organization's data. One of the best ways to prevent that from happening is to keep your backup server patched and updated. It is equally important, however, to keep application servers up to date to prevent a protected resource from acting as a point of entry for a hacker who wants to break into your backup server.








