
Henrik Dolle - Fotolia
What does your backup and recovery audit checklist need?
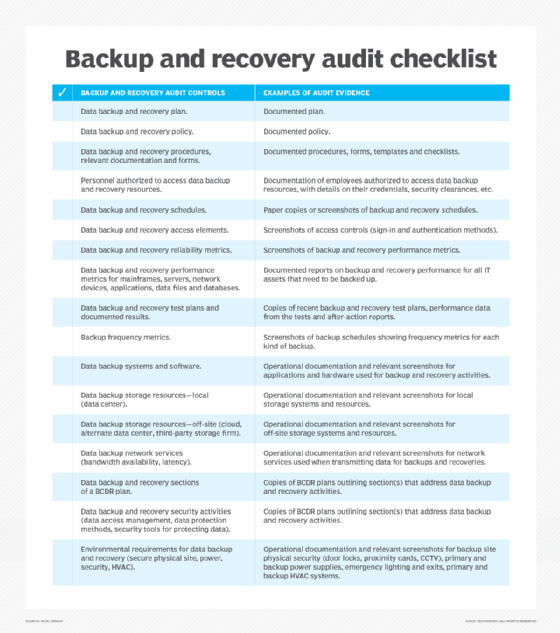
This backup and recovery audit checklist offers a comprehensive group of controls and evidence examples to get you ready for the important process of IT auditing.
To ensure that data backup activities are consistent with good practice and relevant standards and regulations, periodic audits are important.
Audits ensure you're performing backups regularly using good backup practices, your backup systems and storage resources perform correctly, and you're following all relevant controls. If the organization has policies and procedures in place regarding data backup and recovery activities, audits provide evidence to senior management, as well as external organizations -- regulators, key customers and stakeholders, for example -- that the organization conducts its data protection programs properly.
It's best to have a backup and recovery audit checklist of items, like the one below, to make certain you're taking care of everything. You don't want to leave anything out when it comes to the mission-critical task of backup and recovery.
When preparing for a backup and recovery audit, you must address several important factors.
First, identify the backup and recovery controls that you must likely audit. If you use an internal or external auditor, ensure the audit team knows how to audit IT systems. Determine which IT department team should support the audit. Establish a work area for the audit team. Secure a variety of documents, reports and other information as evidence for examination by the auditors.
The following backup and recovery audit checklist itemizes the various controls that might be audited. This way, you can be prepared for most audit requests. In the end, this work helps facilitate the timely completion and delivery of the audit report.
When going over your backup and recovery audit checklist, err on the side of more evidence, rather than less. More audit findings means more remediation work once the audit report has been approved and published. Your organization will likely circulate the audit report to senior IT and corporate management, so plenty of relevant evidence goes a long way.






