
maxkabakov - Fotolia
Asigra Cloud Backup piles on extra layers of cyberdefense
As cybercriminals circumvent immutable backup by stealing admin credentials, Asigra 14.2 counters with Deep MFA, asking for permission whenever changes to backup policies are made.
(This story was updated Dec. 15, 2020)
Asigra's new deep multi-factor authentication feature isn't satisfied with just checking IDs at the door.
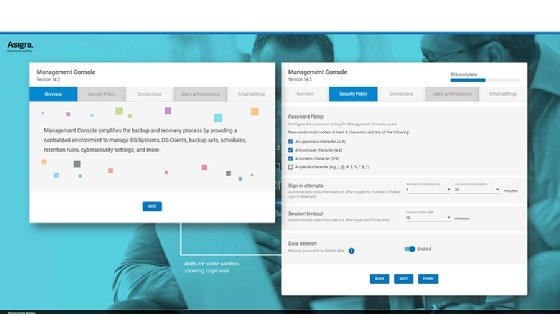
Asigra rolled out a version 14.2 of its Cloud Backup software in August with a feature called Deep MFA. Deep MFA checks for permissions at key points to prevent bad actors from compromising backups. Customers can set MFA for activities that affect the primary backup repository, such as logging in, emptying the trash and changing how long the trash retains data. The MFA Setup Wizard guides management console users through the initial configuration of users and permissions as well as notifications and alert settings. From there, users can manage and save credentials to avoid manually entering them each time.
Asigra upgraded its Deep MFA feature today to protect Microsoft 365 data. As with the primary backup repository, Asigra Deep MFA will prompt for authentication when users try to access sensitive application functions, such as deleting mailboxes or changing retention policies. Asigra executive vice president Eran Farajun said Asigra is now working on extending Deep MFA's capabilities to Salesforce, G-Suite and Kubernetes backup data.
Deep MFA is app-centric and passwordless, reducing the inconvenience of extra security checks. Administrators can use the fingerprint or face recognition capabilities of their mobile devices to authenticate without using a password. This also provides an extra layer of security, as cybercriminals are less likely to get ahold of biometrics.
Asigra customers get Deep MFA with Asigra Cloud Backup 14.2 at no additional charge.
Farajun said Deep MFA is the latest in the "cat-and-mouse game" of IT organizations against cybercriminals. He said there is a constant back-and-forth arms race where the "good guys" come up with ways to protect data against breaches and the "bad guys" find ways to circumvent defenses. Many backup vendors now have the capability to make their backups immutable, preventing unauthorized deletion. However, criminals have started getting around immutable backup by stealing the credentials of backup operators. Because they can't change what's in the backups, the attackers compromise them through the backup software by changing retention and deletion settings.
"They're using the backup software against itself," Farajun said.
Deep MFA can prevent this by making it harder for an attacker to change settings. An administrator must approve or deny the changes, which they can do from their phone via biometrics. Retention policy changes should be relatively infrequent, making it easier to identify a potential breach when administrators get authentication requests for changes they didn't ask for. Farajun said Deep MFA adds extra steps to breaching an Asigra-based backup system, hopefully enough to deter an attacker and make them go after someone else.
Backup vendors have been adding heightened security measures to their software. Farajun praised its competitor and cyber protection vendor Acronis for sending a clear market message about the importance of security in backup processes. He also said Rubrik and Cohesity have done a good job pushing immutable backup, which was the perfect counter to cybercriminals deleting backups.
Marc Staimer, president of Dragon Slayer Consulting, said Asigra's Deep MFA is similar to Cobalt Iron's Cyber Shield, and they are so far the only two backup vendors he knows of that provide deep layers of authentication. Most MFA is treated like single sign-on, which he said "only guards the front door." Having to authenticate again whenever anyone does anything that could impact the data prevents attacks that subvert immutable storage. Staimer said it is a good counter to the latest ransomware threat, but it's only a matter of time before cybercriminals come up with a new one.
"A new generation of ransomware is attacking immutable storage," Staimer said. "It blocks this type of attack, but there will be others."
Staimer warned that human behavior is always a potential weak spot in any cybersecurity measures. He said MFA needs to be as unobtrusive to users as possible. That is why the passwordless and biometrics component of Asigra's Deep MFA is so important. If the ransomware defense is too inconvenient, users won't implement it.
Luckily, the convenience factor applies to criminals, too, said Staimer. Cybercrime is a lucrative business, and like with legitimate businesses, time is money. Attackers want easy targets and won't waste their time jumping through multiple hoops. Therefore, no security measures need to be perfect, which Staimer said is impossible anyway. Cyberdefense only needs to be inconvenient enough for bad actors that they go after someone else.
"It's a situation where you don't need to be faster than the bear -- just faster than your friends," Staimer said.






